Projects/Netlight
| Project: Netlight | |
|---|---|
| Beschrijving | The network traffic light at haxogreen |
| Start | 2012-07-27 |
| Contact | Pietdv |
| Status | Production |
Because of a faulty switch the network at haxogreen 2012 was quite buggy for a while. After a couple of hours we were sick of opening up a terminal and starting a ping to check if the internet was up. We had a raspi and a traffic light available, so we started hacking. We made a little relay board to let the raspi control the traffic light, and wrote a shell script to check if there was an internet connection and set the traffic light to green if there was, to red if there wasn't.
http://www.youtube.com/watch?v=uxdJv-h0Fks
Update 28/07/12
We made a new relay board so we can control the two light independently, When the raspi is booting both lights are now off.
Update 28/07/12 nr2
We ported the code to Python. When there is only a limited amount of package loss, the lights now blinks.
People who helped
Gallery
-
Raspberry PI with a relay board connected to it
-
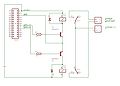
The schematic of the relay board
Script
#!/usr/bin/env python
"""
A pure python ping implementation using raw socket.
Note that ICMP messages can only be sent from processes running as root.
Derived from ping.c distributed in Linux's netkit. That code is
copyright (c) 1989 by The Regents of the University of California.
That code is in turn derived from code written by Mike Muuss of the
US Army Ballistic Research Laboratory in December, 1983 and
placed in the public domain. They have my thanks.
Bugs are naturally mine. I'd be glad to hear about them. There are
certainly word - size dependenceies here.
Copyright (c) Matthew Dixon Cowles, <http://www.visi.com/~mdc/>.
Distributable under the terms of the GNU General Public License
version 2. Provided with no warranties of any sort.
Original Version from Matthew Dixon Cowles:
-> ftp://ftp.visi.com/users/mdc/ping.py
Rewrite by Jens Diemer:
-> http://www.python-forum.de/post-69122.html#69122
Rewrite by George Notaras:
-> http://www.g-loaded.eu/2009/10/30/python-ping/
Revision history
22:16, 28 July 2012 (CEST)22:16, 28 July 2012 (CEST)22:16, 28 July 2012 (CEST)~
November 8, 2009
----------------
Improved compatibility with GNU/Linux systems.
Fixes by:
* George Notaras -- http://www.g-loaded.eu
Reported by:
* Chris Hallman -- http://cdhallman.blogspot.com
Changes in this release:
- Re-use time.time() instead of time.clock(). The 2007 implementation
worked only under Microsoft Windows. Failed on GNU/Linux.
time.clock() behaves differently under the two OSes[1].
[1] http://docs.python.org/library/time.html#time.clock
May 30, 2007
------------
little rewrite by Jens Diemer:
- change socket asterisk import to a normal import
- replace time.time() with time.clock()
- delete "return None" (or change to "return" only)
- in checksum() rename "str" to "source_string"
November 22, 1997
-----------------
Initial hack. Doesn't do much, but rather than try to guess
what features I (or others) will want in the future, I've only
put in what I need now.
December 16, 1997
-----------------
For some reason, the checksum bytes are in the wrong order when
this is run under Solaris 2.X for SPARC but it works right under
Linux x86. Since I don't know just what's wrong, I'll swap the
bytes always and then do an htons().
December 4, 2000
----------------
Changed the struct.pack() calls to pack the checksum and ID as
unsigned. My thanks to Jerome Poincheval for the fix.
Last commit info:
22:16, 28 July 2012 (CEST)22:16, 28 July 2012 (CEST)22:16, 28 July 2012 (CEST)~~
$LastChangedDate: $
$Rev: $
$Author: $
"""
import os, sys, socket, struct, select, time
# From /usr/include/linux/icmp.h; your milage may vary.
ICMP_ECHO_REQUEST = 8 # Seems to be the same on Solaris.
IP="8.8.8.8"
TIMEOUT=0.4
GREENPIN=24
REDPIN=23
HISTORY=10
def checksum(source_string):
"""
I'm not too confident that this is right but testing seems
to suggest that it gives the same answers as in_cksum in ping.c
"""
sum = 0
countTo = (len(source_string)/2)*2
count = 0
while count<countTo:
thisVal = ord(source_string[count + 1])*256 + ord(source_string[count])
sum = sum + thisVal
sum = sum & 0xffffffff # Necessary?
count = count + 2
if countTo<len(source_string):
sum = sum + ord(source_string[len(source_string) - 1])
sum = sum & 0xffffffff # Necessary?
sum = (sum >> 16) + (sum & 0xffff)
sum = sum + (sum >> 16)
answer = ~sum
answer = answer & 0xffff
# Swap bytes. Bugger me if I know why.
answer = answer >> 8 | (answer << 8 & 0xff00)
return answer
def receive_one_ping(my_socket, ID, timeout):
"""
receive the ping from the socket.
"""
timeLeft = timeout
while True:
startedSelect = time.time()
whatReady = select.select([my_socket], [], [], timeLeft)
howLongInSelect = (time.time() - startedSelect)
if whatReady[0] == []: # Timeout
return
timeReceived = time.time()
recPacket, addr = my_socket.recvfrom(1024)
icmpHeader = recPacket[20:28]
type, code, checksum, packetID, sequence = struct.unpack(
"bbHHh", icmpHeader
)
if packetID == ID:
bytesInDouble = struct.calcsize("d")
timeSent = struct.unpack("d", recPacket[28:28 + bytesInDouble])[0]
return timeReceived - timeSent
timeLeft = timeLeft - howLongInSelect
if timeLeft <= 0:
return
def send_one_ping(my_socket, dest_addr, ID):
"""
Send one ping to the given >dest_addr<.
"""
dest_addr = socket.gethostbyname(dest_addr)
# Header is type (8), code (8), checksum (16), id (16), sequence (16)
my_checksum = 0
# Make a dummy heder with a 0 checksum.
header = struct.pack("bbHHh", ICMP_ECHO_REQUEST, 0, my_checksum, ID, 1)
bytesInDouble = struct.calcsize("d")
data = (192 - bytesInDouble) * "Q"
data = struct.pack("d", time.time()) + data
# Calculate the checksum on the data and the dummy header.
my_checksum = checksum(header + data)
# Now that we have the right checksum, we put that in. It's just easier
# to make up a new header than to stuff it into the dummy.
header = struct.pack(
"bbHHh", ICMP_ECHO_REQUEST, 0, socket.htons(my_checksum), ID, 1
)
packet = header + data
my_socket.sendto(packet, (dest_addr, 1)) # Don't know about the 1
def do_one(dest_addr, timeout):
"""
Returns either the delay (in seconds) or none on timeout.
"""
icmp = socket.getprotobyname("icmp")
try:
my_socket = socket.socket(socket.AF_INET, socket.SOCK_RAW, icmp)
except socket.error, (errno, msg):
if errno == 1:
# Operation not permitted
msg = msg + (
" - Note that ICMP messages can only be sent from processes"
" running as root."
)
raise socket.error(msg)
raise # raise the original error
my_ID = os.getpid() & 0xFFFF
send_one_ping(my_socket, dest_addr, my_ID)
delay = receive_one_ping(my_socket, my_ID, timeout)
my_socket.close()
return delay
def verbose_ping(dest_addr, timeout = 2, count = 4):
"""
Send >count< ping to >dest_addr< with the given >timeout< and display
the result.
"""
for i in xrange(count):
print "ping %s..." % dest_addr,
try:
delay = do_one(dest_addr, timeout)
except socket.gaierror, e:
print "failed. (socket error: '%s')" % e[1]
break
if delay == None:
print "failed. (timeout within %ssec.)" % timeout
else:
delay = delay * 1000
print "get ping in %0.4fms" % delay
print
def set_pin(pin,value):
file('/sys/class/gpio/gpio'+str(pin)+'/value','w').write(str(value))
def blink_pin(pin,f):
t=time.time()
t=t-int(t)
if t < 0.5:
set_pin(pin,1)
else:
set_pin(pin,0)
def init_pin(pin):
file('/sys/class/gpio/export','w').write(str(pin))
file('/sys/class/gpio/gpio'+str(pin)+'/direction','w').write('out')
if __name__ == '__main__':
count=0
loss=0
init_pin(REDPIN);
init_pin(GREENPIN);
while 1 == 1:
lasttime=time.time()
print time.time()
if count>(HISTORY-1):
count=count-1
if loss>(HISTORY-1):
loss=loss-1
ping = None
try:
ping = do_one(IP,TIMEOUT)
except:
pass
count=count+1
if ping == None:
loss=loss+1
elif loss>0:
loss=loss-1
print "ping "+str(count)+", loss "+str(loss)
if loss==0:
set_pin(REDPIN,0)
set_pin(GREENPIN,1)
elif loss==count:
set_pin(GREENPIN,0)
set_pin(REDPIN,1)
else:
set_pin(GREENPIN,1)
blink_pin(REDPIN,0.2+((1.0-(float(loss)/float(count)))/2.0))
wait = lasttime+1 - time.time()
print wait
if loss==0 and wait:
time.sleep(wait)